Email Spoof For Fun Only
PHP / HTML script
This method is easy to use if you have your own hosting space (ie you have a website). This works on a few hosting sites I tested. Thanks to Sethioz for some of the code.
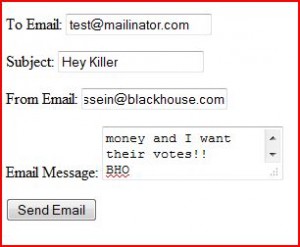
This basically sets up a form where you enter the fake email address, subject, and who you want to send it to. The form then uses a script to actually send it.
NOTE: SMTP and PHP have to be supported.
These should be in the same folder. Create a folder in your server. Many sites use cPanel. If so you can go to the file manager and create new folder. Now create two new files:
Name one index.html and the other spoof.php
put this code in index.html:
<form action="spoofer.php" method="GET"> <p>To Email: <input type="text" name="email" /></p> <p>Subject: <input type="text" name="header" /></p> <p>From Email: <input type="text" name="fake" /></p> <p>Email Message: <textarea name="message"></textarea></p> <p><input type="submit" value="Send Email"></p> </form>
Save it and put this code inside spoofer.php:
<?php
if (!isset($_GET[email]) || empty($_GET[email]))
{
echo "TO field is empty";
exit;
}
else
{
$to = $_GET[email];
}
if (!isset($_GET[header]) || empty($_GET[header]))
{
echo "Subject is missing";
exit;
}
else
{
$subject = $_GET[header];
}
if (!isset($_GET[fake]) || empty($_GET[fake]))
{
echo "FROM email address is missing";
exit;
}
else
{
$fake = $_GET[fake];
}
if (!isset($_GET[message]) || empty($_GET[message]))
{
echo "email message box is empty";
exit;
}
else
{
$message = $_GET[message];
}
$headers = "MIME-Version: 1.0" . "\r\n";
$headers .= "Content-type:text/html;charset=iso-8859-1" . "\r\n";
$headers .= "From: " . $fake . " <" . $fake . ">" . "\r\n";
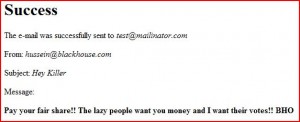
if (mail($to, $subject, $message, $headers))
{
echo"<h1>Success</h1>\n";
echo"<p>The e-mail was successfully sent to <i>" . $to . "</i></p>\n";
echo"<p>From: <i>" . $fake . "</i></p>\n";
echo"<p>Subject: <i>" . $subject . "</i></p>\n";
echo"<p>Message:</p>\n";
echo"<p><b>" . $message . "</b></p>";
}
else
{
echo"<h1>Error!</h1>\n";
echo"<p>The mail() function failed.</p>";
}
?>
Now save that and go to your site where you created the folder. For example, www.mysite.com/spoofedemail/ You should see the form pop up. Now test it on your address. Please note, your real address will show up in the header and anyone with more than cursory computer knowledge will know how to see that.
Final Note: use at your own risk. This site nor anyone else is responsible for anything stupid you do with this script.